
Featured Article
Investment Scams: The Rising Threat in the World of Fraud

A Complete Guide to Accepting EMV Payments
Wondering about EMV Payments? We explain what EMV cards are, how they work, and how they help reduce fraudulent activity.

Payments Fraud: 3 Best Practices for Cybersecurity Awareness Month & Beyond
Letting Cybersecurity Awareness Month go by without implementing 5 best practices for protecting against payments fraud could lead to frightening results.

Top Strategies for Risk-Based Transaction Monitoring
What Is Risk-Based Transaction Monitoring? Transaction monitoring refers to the monitoring of all customer transactions. A risk-based approach requires more intensive monitoring for clients or scenarios that have a higher risk.
Enhancing Account Takeover Detection With Identity-centric, Biometric Protections
Account takeover (ATO) attacks now account for more than $16 billion in annual losses in the just US alone.Account takeover (ATO) attacks now account for more than $16 billion in annual losses in the just US alone.

Fraud Investigation: Simply Explained
Wondering about fraud investigation? We explain all aspects of fraud investigation, from determining whether a fraud has occurred to the resolution.
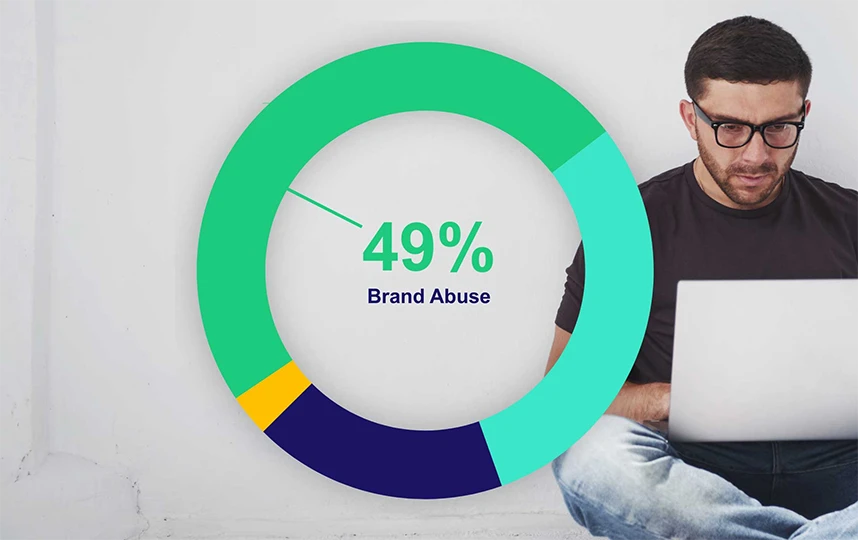
Outseer Report: Nearly Half of All Cyberattacks Involve Brand Impersonation
According to the latest quarterly analysis from Outseer's FraudAction team, brand impersonation scams continue to exploit the sharp rise in digital banking.

Payment Security: Everything You Need to Know
We explain all aspects of payment security, steps you can take to protect your organization and your customers, and the obligations you are responsible for.






